Have you heard of the podcast Darknet Diaries? Well if you made it to my blog, you either have or you should. If you’ don’t know of or never heard of Darknet Diaries, go ahead and check them out, I promise you won’t be disappointed. Its a podcast created and hosted by Jack Rhysider that explores the world of Cybersecurity, Hacking, and Cybercrime.
Anyways, on this podcast there is an episode, number 48 to be exact, Operation Socialist is the name. In this episode, an NSA tool by the name of “Quantum Insert” is mentioned. I’ll take a quote directly from Jack in this episode:
This Quantum Insert is amazing. Allow me to geek out on it for a moment. First step is to clone the LinkedIn website and that’s not so hard; with the right software, it’s a few keystroke commands and you’re done. Then you need to put malicious software on this cloned website so if someone visited it, they would be infected. The only complicated part about this step is to know what version of software your target is running so you can exploit their machine if they visit the link. But once you know that, this step is easy, too.
But here’s where things get crazy; if the hackers had access to a router in between the victim and LinkedIn, then the hackers could then see that web traffic between the victim and LinkedIn. What Quantum Insert does, is it uses that router to split the request to LinkedIn into two separate requests; one going to the real LinkedIn site and the other going to this fake LinkedIn site that the hackers own. What has to happen for the attack to work is that the fake LinkedIn site has to respond quicker than the real one which then delivers the malicious software to the victim’s machine who’s none the wiser because there’s literally no way they can tell it’s not the real LinkedIn site. The URL says LinkedIn, the SSL cert is signed, the site looks like LinkedIn. Even all their friends and posts are there. It’s just, this rogue website injected some malicious software into the real one by splitting the traffic at the router. It’s really quite incredible.
Source: Darknet Diaries
And there you have it. Jack broke it down pretty simply here, but you get the general idea. When I first heard of this sort of attack I was intrigued to say the least. So I decided to do some research on this Nation-State level attack and write this post here about it.
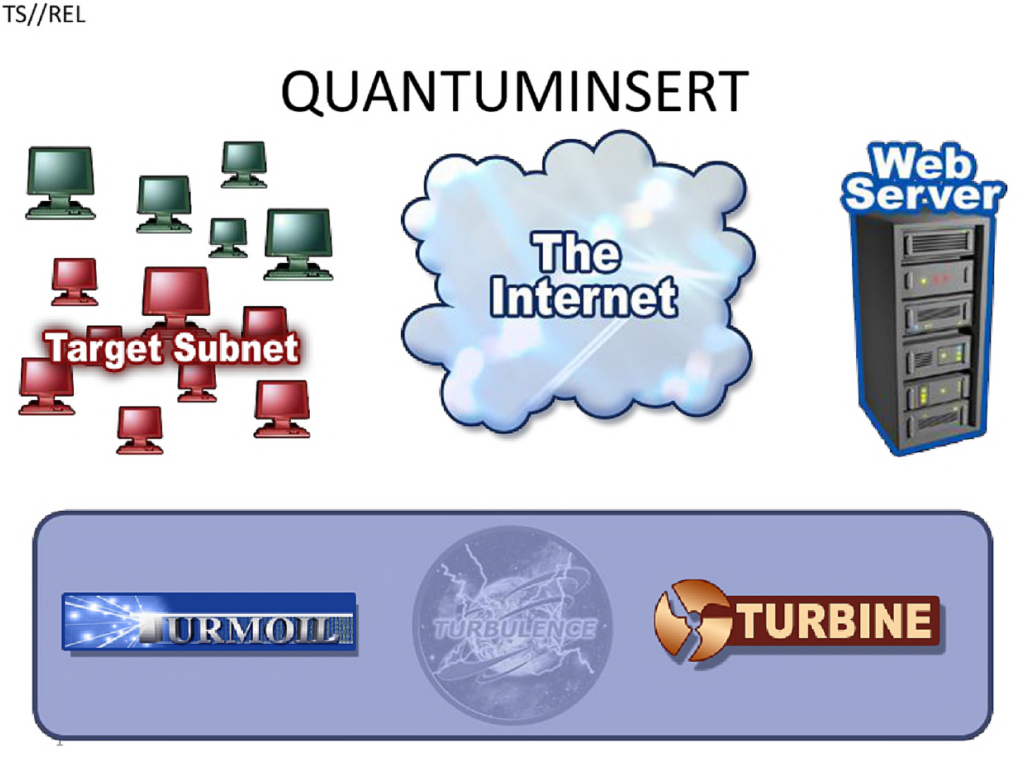
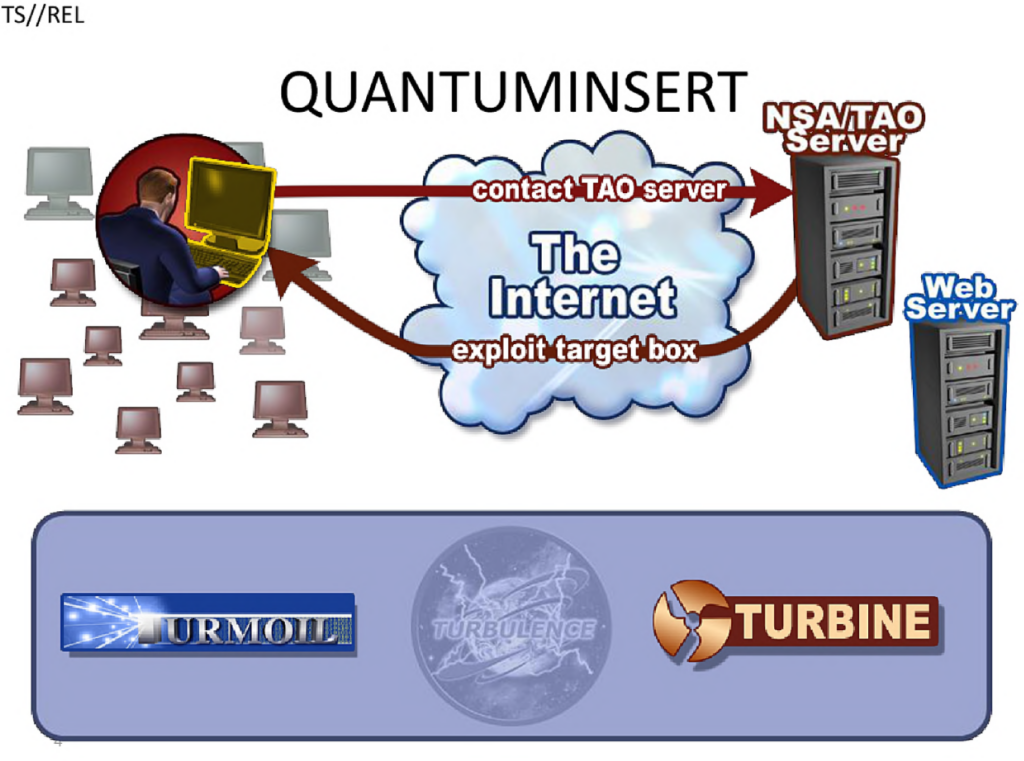
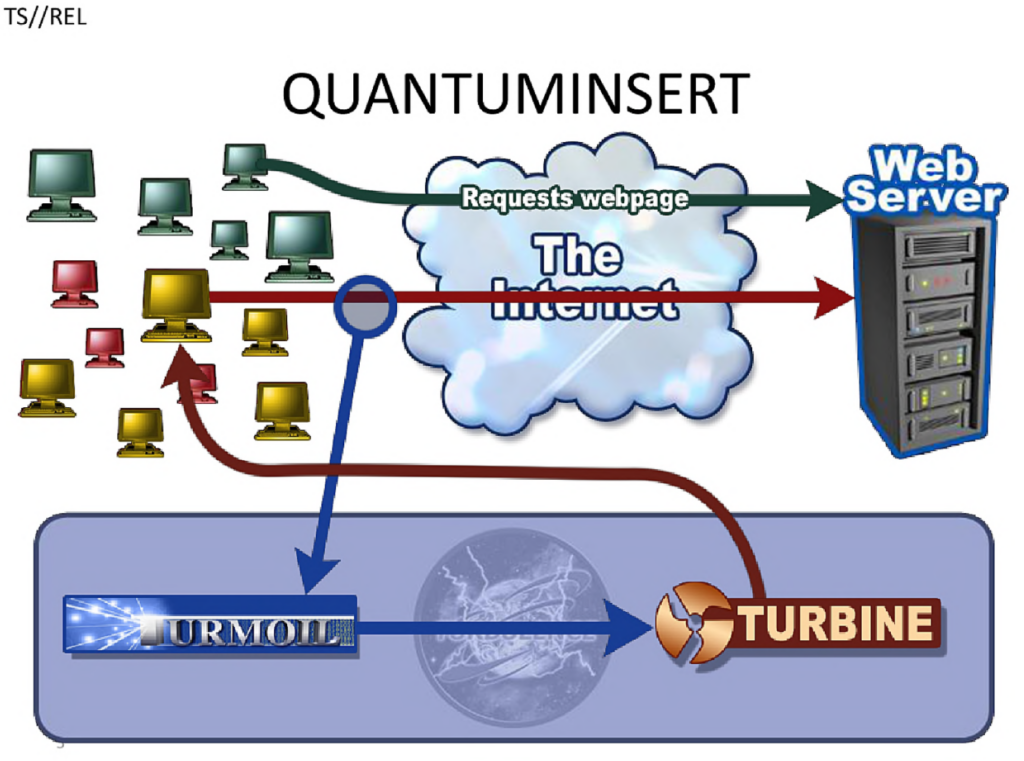
Quantum Insert is part of a suite of Quantum Tools owned and operated by the NSA. The organization deploys these suite of tools against targets around the world. Initial information about Quantum Insert was leaked by Edward Snowden. We have since found more about this tool, how it works and what it is capable of. Here I found some leaked diagrams hosted by the American Civil Liberties Union that I will later use in this blog post to serve as a visual representation aid.
Quantum Insert involves high-speed TCP packet injection to hijack a user’s web request and deliver a malicious payload before the legitimate response arrives. This technique has been used for targeted espionage against individuals, governments, and corporations.
Let’s dive into it, shall we?
Understanding the Terminology
Here are some key phrases used to describe some of the infrastructure involves in this type of attack:
Turbulence – Framework that includes tools such as Quantum Insert, Turmoil, Turbine, etc.
Turbine – Automated Cyber operations platform used to facilitate and manage attacks more effectively.
Quantum Insert – Advanced attack that hijacks web traffic and redirects targets.
Turmoil – Packet interception system that passively monitors internet traffic in real-time.
Validator – Tool that confirms successful infections and establishes remote access.
Foxacid – Server-based exploit platform used by the NSA to deliver malware and remote access tools to compromised targets.
XKeyScore – Massive digital surveillance search engine used by the NSA to collect, analyze, and search internet traffic in real-time.
Tailored Access Operations (TAO) – NSA’s elite Cyber-Espionage division.
Once you have a better understanding of these terms, grasping the stages of the attack will become more clear.
Now to better understand Quantum Insert, let’s break it down into categories:
The Core Concept of Quantum Insert
What is a Quantum Insert Attack?
Quantum Insert is a man-on-the-side (MOTS) as opposed to a man-in-the-middle (MITM) attack that exploits the speed of packet injection to serve a fake webpage, email, or file before the legitimate source can respond.
It allows the attacker to:
- Hijack an HTTP request before the actual server can reply.
- Inject a malicious payload into the response.
- Compromise the target system without their knowledge.
How Does It Work?
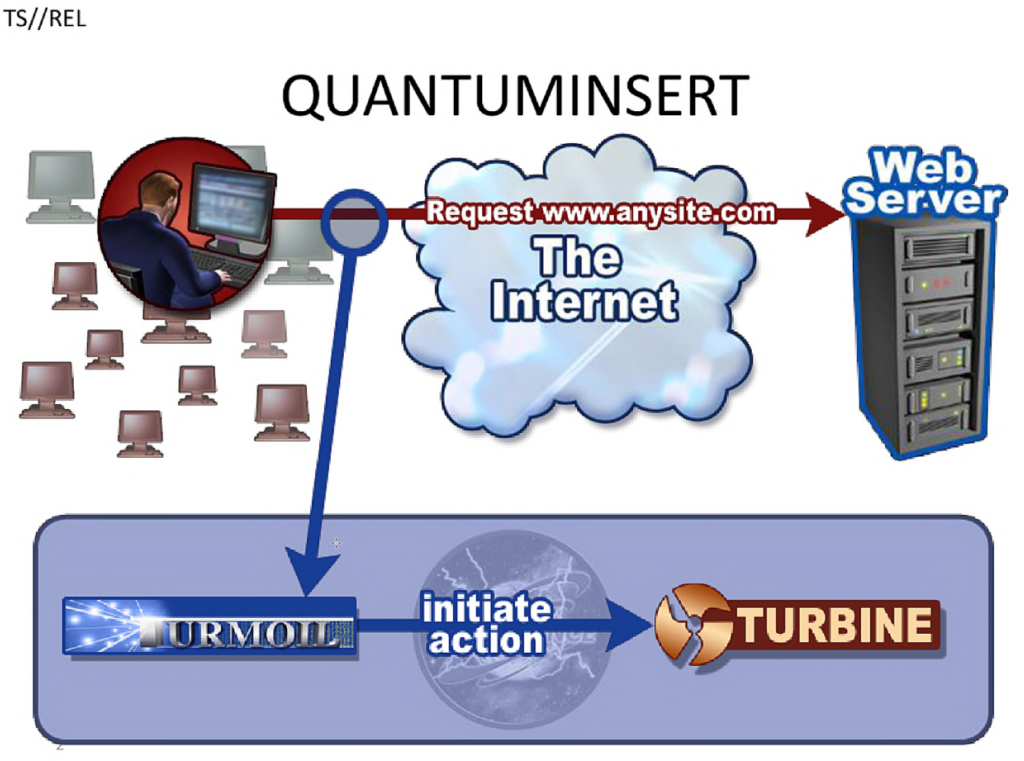
- A target visits a legitimate website (e.g., a news, social media, government sites, etc.).
- The request travels through the internet and is monitored using tools like Turmoil.
- The NSA’s Quantum system races to respond (faster than the actual website).
- The victim unknowingly receives the NSA’s response instead of the real website.
- The injected malicious content exploits the browser and allows remote access.
This attack is particularly effective because most web traffic (HTTP) is unencrypted, making it easy to intercept and manipulate. It is important to note that this attack wouldn’t work on encrypted traffic, but there are ways around this such as deploying a Downgrade or SSL Stripping attack.
The Attack Chain
Reconnaissance
The adversary identifies their target and begins to monitor internet traffic at key network points, such as ISPs or backbone routers.
Specific identifiers, like IP addresses or tracking cookies, are used to pinpoint the desired victim’s web requests. Employing bulk data collection systems (such as XKEYSCORE) to filter out relevant data based on their browsing habits or accessed services.
At this stage, the attackers gather intelligence on the victim’s online behavior, allowing them to predict when and where a Quantum Insert attack will be most effective.
Preparing for the Attack
The adversary passively observes their victim’s browsing activity, waiting for the right moment to inject a malicious response.
This involves strategies such as:
Watching outbound HTTP requests for specific destinations (e.g., LinkedIn, webmail services, or government portals).
Timing the attack precisely, ensuring the malicious response reaches the target before the legitimate one.
Payload Delivery and Exploitation
With the victim’s connection hijacked, the attacker redirects their browser to a Foxacid server (NSA’s payload delivery servers).
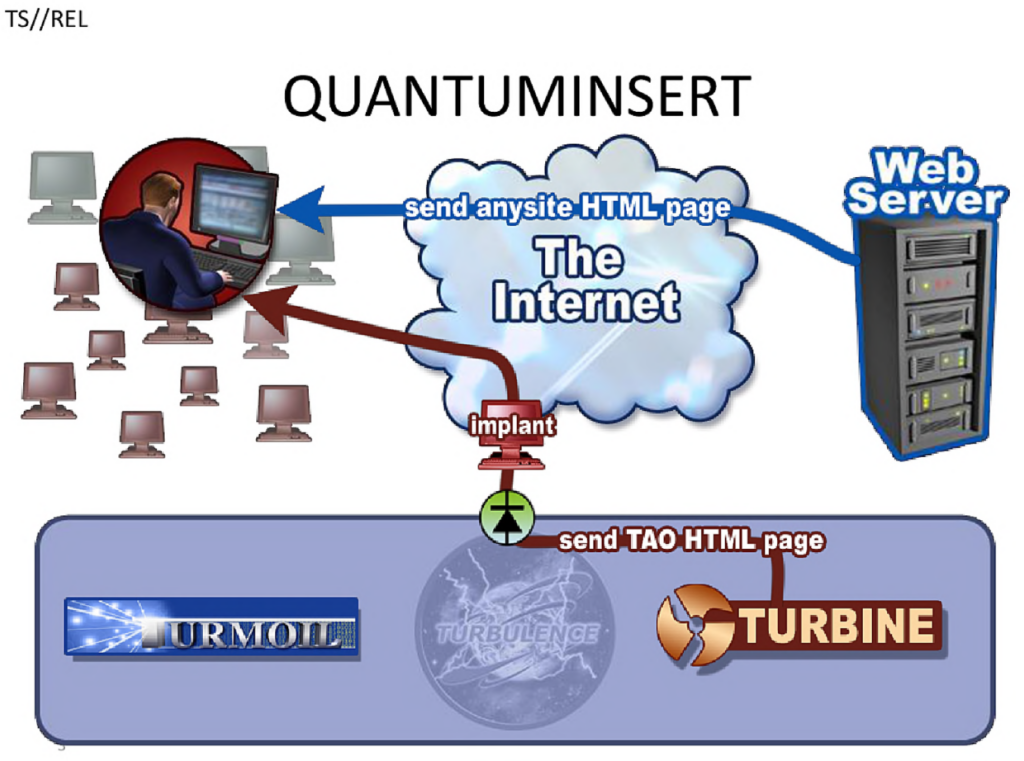
The adversary now:
- Delivers a tailored exploit, typically based on browser or software vulnerabilities.
- Deploys malware or backdoors, granting persistent access to the victim’s system.
- Extracts sensitive data, such as login credentials, encryption keys, or classified documents.
Once the payload is successfully executed, the victim remains compromised without ever suspecting interference. The attacker now has long-term access to the system, enabling espionage, surveillance or further attacks.
Key Components of Quantum Insert
Network Positioning and Passive Surveillance
To execute a Quantum Insert attack, the NSA relies on upstream surveillance and strategic internet backbone access.
This means that the NSA has access to major telecommunication networks, which shouldn’t be a surprise to anyone. They use bulk metadata collection (using tools such as XKeyScore) to identify high-value targets. They also deploy network tapping at crucial points to monitor and manipulate traffic. This access allows NSA and its partners (like GCHQ) to watch for a victim’s web requests in real-time.
Quantum Servers
The Quantum Insert system operates through a network of strategically placed high-speed servers capable of injecting packets before the real response arrives. This includes a combinations of tools as mentioned above (Turbulence Framework). These tools work together to prepare, mount and execute the attacks.
Exploits and Payloads
Once the Quantum Insert attack succeeds, the target is redirected to an exploit server that hosts malicious payloads. These exploits are designed to infect the victim’s browser. They then deploy remote access trojans (RATs) and exfiltrate sensitive data.
GCHQ (UK intelligence) referred to these operations as “Man on the Side” attacks, meaning the attacker can observe and modify traffic but does not fully control the connection. There are also several mentions of these terminology in other leaked documentation.
Real-World Examples of Quantum Insert Attacks
Several high-profile attacks have been linked to Quantum Insert:
Belgacom Hack (Operation Socialist)
The Belgacom hack targeted an EU telecommunications provider. GCHQ used Quantum Insert to hijack LinkedIn and Slashdot visits of specific Belgacom engineers. They then injected malware into their computers to gain persistent access to the telecom network.
Attacks on Chinese Institutions
Leaks also suggest that Quantum Insert was used against China, including the Chinese Ministry of Public Security and the China Telecom network.
Attacks on International Conferences
Quantum Insert has been used against individuals attending conferences such as G20 summits and economic forums. These attacks targeted diplomats, journalists, and corporate executives.
Detection and Mitigation Strategies
Detecting Quantum Insert
Since Quantum Insert relies on packet injection, some techniques can help detect it. Latency analysis is a key player here; Look for responses that arrive slightly faster than expected, followed by a legitimate response shortly after. You can also utilize a Network Intrusion Detection Systems (NIDS) and take advantage of monitoring tools like Suricata or Zeek (Bro IDS), which can help detect anomalous injected packets.
Preventing Quantum Insert
Use HTTPS Everywhere! This is the most effective defense. This attack relies heavily on the traffic being unencrypted.
Monitor network traffic for anomalies. Unexpected redirects or duplicate responses can indicate interference, so be vigilant of those. Additionally, its crucial to implement HTTP Strict Transport Security (HSTS) which forces HTTPS connections, making it impossible for an attacker to hijack HTTP requests. This would make it impossible to force a downgrade attack. And lastly, many Quantum Insert attacks rely on browser vulnerabilities, so keep software up to date!
Shoutouts
Special thanks to Jack Rhysider for creating Darknet Diaries and inspiring this post. Also as special thanks to Edward Snowden and WikiLeaks for contributing the diagrams used in this post. Final thanks to all of the external sources that made this post possible.