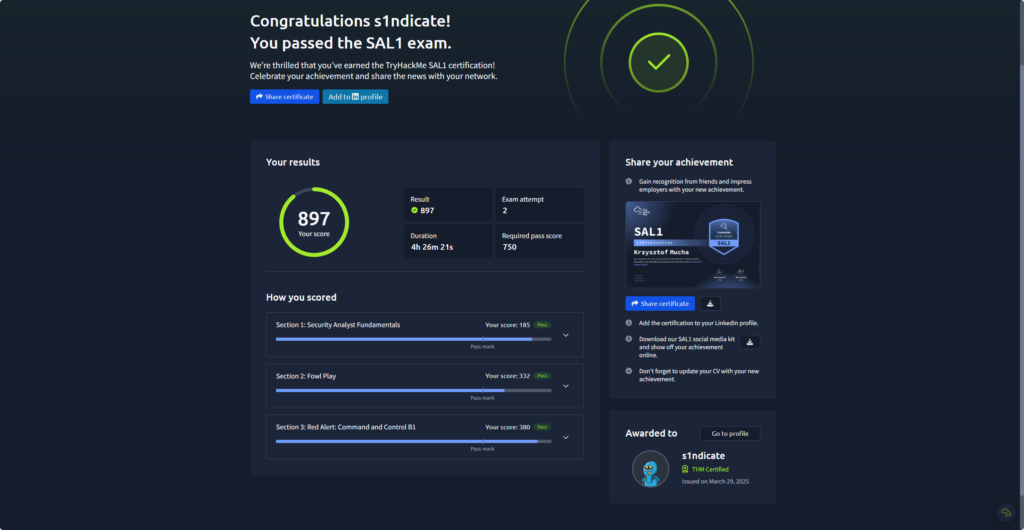
For the month of March, TryHackMe was offering free exam vouchers for their new SAL1 (Security Analyst Level 1) exam to holders of the BTL1 or CySA+ certifications. Since I am a current holder of the CySA+, I was able to seize this opportunity and take an attempt at this certification.
Quick Side Note: This is my brutally honest opinion. While I did receive a free exam voucher, I have no affiliation with TryHackMe beyond being a regular user of their platform.
What is the SAL1?
Here’s what TryHackMe has to say about the certification:
What is the SAL1 Certification?
Prove your skills in a real-world virtual SOC with TryHackMe’s SAL1 certification, tackling practical scenarios inside our SOC Simulator (a virtual security operations centre).
SAL1 is more than just a certification, it’s a real-world assessment that validates your ability to work as a security analyst. Prove your skills in a real-world virtual SOC with TryHackMe’s SAL1 certification, tackling practical scenarios inside our SOC Simulator that allows you to analyse alerts, escalate incidents, and generate reports just like a real security analyst professional.
What you’ll learn & prove:
- Threat analysis – Identify and investigate cyber threats in a live SOC environment
- Incident triage & escalation – Decide when and how to escalate security incidents
- Report generation – Master the skill of writing SOC reports, a crucial yet overlooked requirement for SOC Analysts
- Cyber security fundamentals – Covering OS basics, networking fundamentals, and core security principles.
Why we developed SAL1
The cyber security job market is competitive, and recruiters need a way to filter for candidates who can hit the ground running. Many aspiring security analysts struggle to gain real-world experience, and hiring managers trying to assess practical skills. We found a common challenge after speaking with countless hiring managers and job seekers. Hiring managers struggle to identify skilled talent while aspiring security analysts find breaking through the noise and proving their abilities difficult.
We built SAL1 to solve these problems by:
- Bridging the gap between knowledge and hands-on expertise
- Establishing a real-world SOC skills benchmark, validated by industry leaders Accenture & Salesforce
- Helping job seekers stand out in a competitive field
- Enabling employers to identify qualified candidates quickly
SAL1 is designed to significantly increase your chances of getting a job and provide a clear pathway into cyber security roles, whether you’re looking for your first job or aiming for a promotion in a SOC role.
Source: TryHackMe

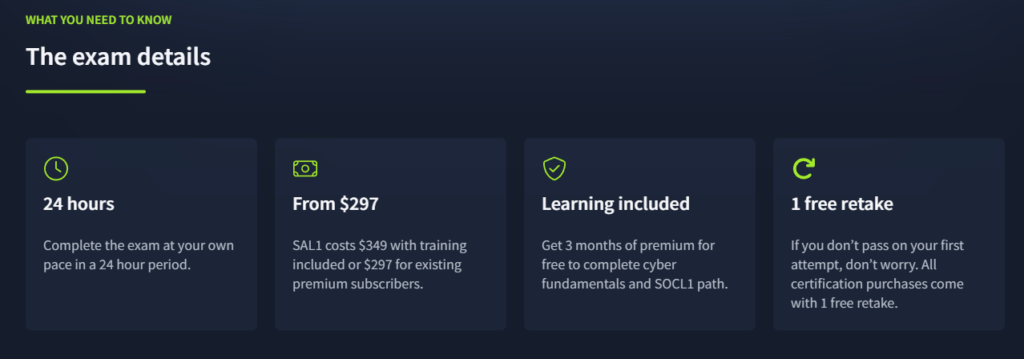
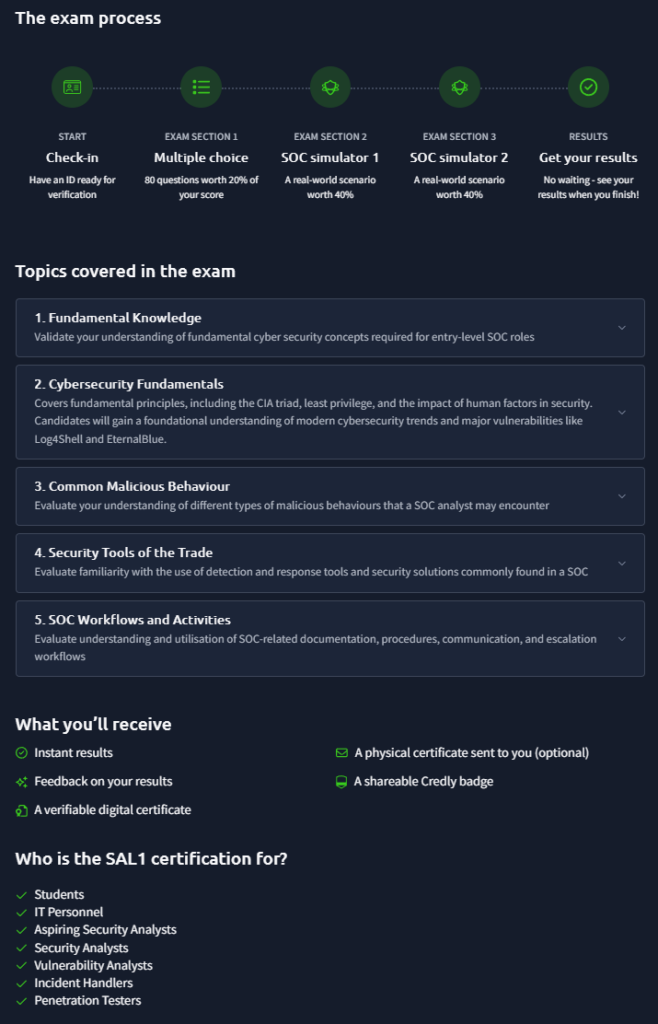
The SAL1 is a mostly practical 24-hour exam that assesses a candidates knowledge and ability to perform the duties of an entry-level SOC Analyst. I say “mostly” because about 20% of the exam consists of multiple-choice questions. I wanted to clarify that this isn’t a fully hands-on exam, there is a small theoretical component as well.
The total time allocated for the exam is 5 hours, consisting of three sections: an 80-question multiple-choice portion with a 60-minute time limit, followed by two SOC simulations, each with a maximum duration of 2 hours. Each section must be completed within its designated time and in the given order. However, you’re free to take breaks between sections, as long as the entire exam is completed within the 24-hour window. Results are delivered instantly, thanks to AI-powered grading.
Pricing for the exam is as follows:
For £299, you get the exam plus three months of TryHackMe premium, giving you full access to all the training you need to succeed. If you need more time, you can extend your training for as little as £12.
Existing TryHackMe premium users can purchase the exam for £255 (15% off). Bulk discounts are also available based on the number of licenses purchased. Many professionals expense the certification through their employer – check if your company offers learning and development reimbursements.
Source: TryHackMe
Prerequisites
TryHackMe recommends completing the Pre-Security, Cyber Security 101, and SOC Level 1 learning paths before attempting the exam. Additionally, a few specific rooms are suggested for extra preparation, including Investigating with Splunk, Benign, Secret Recipe, and of course, the SOC Simulator.
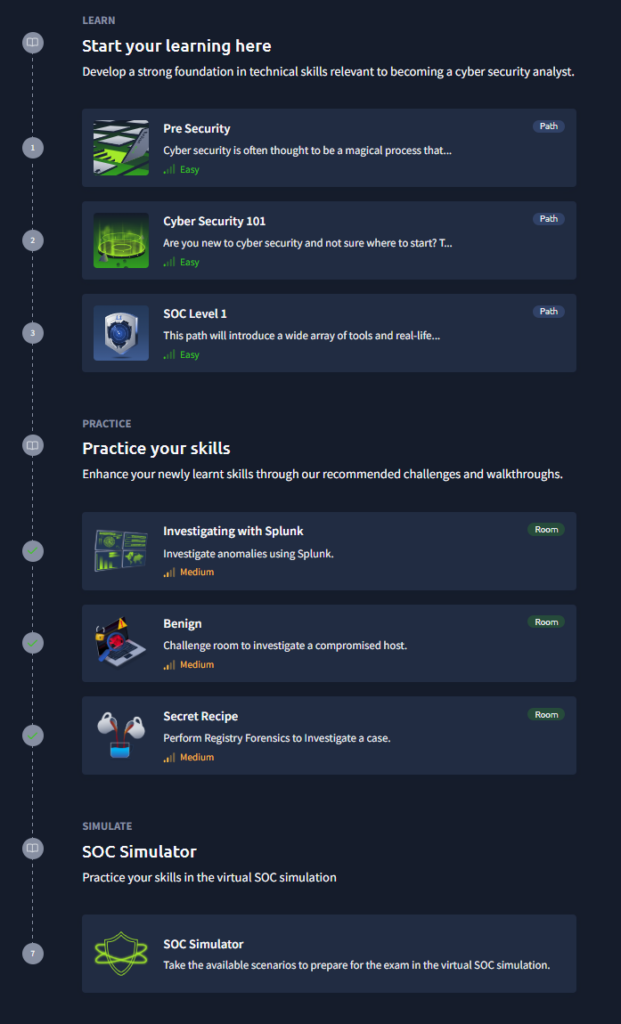
Preparations
As for my preparation, I spent about two hours a day over the course of three days reviewing the material. I had already completed most of the SOC Level 1 path beforehand (ages ago), so I had a general understanding of the topics covered. I went through the remaining content to ensure I had a solid grasp of what to expect from the exam. However, your mileage may vary you may not need to look over the material at all, or you might need to go through the entire learning path, this will vary.
The Exam
The multiple-choice section is quite easy, which makes sense given that this exam is designed for entry-level SOC Analysts. I don’t have any real complaints about this part. It’s also worth noting that TryHackMe offered vouchers to holders of the BTL1 and CySA+ certifications, both of which are more advanced and require a stronger grasp of theoretical knowledge. As a result, those with these certifications will likely find SAL1 more approachable and may not need much additional prep.
Additionally, I want to mention something that stood out to me, though I’m not sure if this was an isolated experience. The platform’s SOC Simulator, surprisingly, performed better than the actual exam. I experienced noticeable latency and delays throughout the exam, from the multiple-choice section to the SOC simulations. This is one area where the exam felt a bit unpolished.
I encountered several technical hiccups, such as alerts not assigning properly and the Analyst VM disconnecting unexpectedly. These issues made the overall experience feel less refined than it could be. That said, I don’t want this to come off as harsh criticism, the exam was still a fantastic experience, and there’s a lot more to unpack. So, let’s keep going…
I highly recommend trying out the SOC Simulator before starting the exam. It gives you a solid idea of how the exam is structured and what the overall experience will feel like on exam day. The layout is nearly identical to the simulator: you have access to an Analyst VM, an Alert Dashboard, and the Splunk SIEM. As the simulation progresses, alerts will come in, and you’ll need to prioritize them based on urgency and age, just like you would in a real SOC environment. However, you’ll primarily rely on the Splunk SIEM, as the Analyst VM doesn’t serve much purpose beyond verifying malicious domains or IPs. This is where your SPL query skills will really come into play. The exam heavily depends on your ability to investigate alerts using the data available in the SIEM. Keep in mind that events occur in real time, so you might not see some activity immediately.
A key to excelling during the simulations is learning to ignore the false positives. Investigating them will not only waste valuable time, but also increase the risk of overlooking or misclassifying a true positive. Once all true positives have been submitted, the simulation ends, so it’s important not to get sidetracked.
Keep in mind that once you submit your final true positive, you can’t go back and make any changes. That’s why it’s crucial to be confident in your submissions and avoid spending time on alerts that don’t show signs of malicious activity.
Recommandations
Firstly, don’t overthink things. After all, this is an entry-level exam and you have everything you need at your disposal to pass. You don’t need any third-party tools or need to leave the exam environment to assist in making a decision. For example, when I first ran through the SOC Simulator, I couldn’t figure out whether an email was malicious. I know, right? It’s because I was overthinking it. I immediately started trying to dig into the email headers, checking for SPF, DKIM, and DMARC results, domain reputation, and all the usual indicators you’d investigate in a real-world scenario. But in this exam, none of this is even possible as you don’t even have that information at your disposal. In fact, it’s much simpler. All you need to do is plug the domain from the email into the scanning tool available inside the VM and it will tell you whether or not the domain or IP is malicious, that’s it! No need for deeper investigative work or external analysis; the answer is right there.
The best approach to this exam is to take your time and stay focused. Try not to stress about the timer, at least not at first and start by carefully reading through all the exam instructions. The countdown begins as soon as you click “Begin,” and the timer is visible in the upper right-hand corner even before the simulation finishes loading.
Do yourself a favor: launch the environment immediately and use the boot-up time to review the exam details and get familiar with the layout. It’s a great opportunity to orient yourself before diving in.
I failed my first attempt (yep, I know), mainly because I didn’t read the directions carefully and let overconfidence get the best of me. What happened? I didn’t escalate all of my alerts properly, and my reporting wasn’t thorough enough. I missed some key pieces of information that would’ve made a huge difference in how I handled the alerts. To make matters worse, I panicked a little when I saw the dreaded timer appear. Instead of carefully reading through the exam environment details, I skimmed them and thought, “Yeah, yeah, I got this, just like the SOC Simulator.”
The problem is, in the SOC Simulator, you’re not graded on your reports. That can give you a false sense of confidence going into the actual exam. Don’t get me wrong, the simulator is a game-changer when it comes to preparation. But don’t overlook the importance of reporting, not just for the exam, but in real-world SOC environments too.
Now with that out of the way, the next thing I recommend is for you to create yourself a template for your reporting. I saved a template in Obsidian that I used for each report I wrote. It outlined specific information for each alert and covered things like impact, IOCs, remediation recommendations, etc. This made it much simpler to write reports. Also on the report writing, don’t jump between alerts and go back and make changes. Take the time on each alert and do it right the first time. This way you won’t be thinking you need to add more information to one alert and end up flipping back between alerts while the exam is going on. This is just a waste of time.
Also, back to the timer, do your best to ignore it. Take your time working through each alert: investigate properly, document thoroughly, report clearly, and then make your submission. If you’ve completed the recommended learning paths, spent time with the SOC Simulator, and follow this advice, you’ll be in good shape.
Lastly, pay attention to the total number of alerts. This becomes especially helpful toward the end of the exam, as it lets you know when all alerts have been received. At that point, your focus should shift to reviewing and submitting any remaining true positives and not waiting for any new alerts to arrive.
As I mentioned earlier, the exam ends the moment you submit your final true positive. That means if you think you’ve submitted everything and all alerts have come in, take a moment to reassess things. Go back and review the alerts. There might be something you saw earlier that felt uncertain, now’s the perfect time to revisit it with fresh eyes and dig a little deeper.
My Feeback
As mentioned earlier, the exam felt a bit unpolished in some areas. There were noticeable performance issues, and at times, it felt more like an extension of the existing SOC Simulator rather than a fully standalone experience. I would’ve liked to see the Analyst VM used for more in-depth investigative work, beyond just checking domains and IP addresses.
It would also be helpful to receive a more detailed breakdown of your performance. I scored fairly well overall, but I missed a couple of escalations. I have a good idea of which ones, but there’s no way to confirm. One of the best ways to grow is by learning from your mistakes, unfortunately, the exam doesn’t currently offer feedback on what you got wrong or how to improve.
Overall, I believe the SAL1 certification is an excellent way to assess a candidate’s ability to perform in a SOC environment. Its focus on practical skills and real-world scenarios makes it a strong option for those looking to demonstrate their readiness for an entry-level SOC Analyst role. While there’s certainly room for improvement, such as expanding the use of the Analyst VM to better evaluate investigative skills (I’m excited to see what SAL2 might bring in that regard).
This could very well mark the beginning of a bright new chapter for TryHackMe. Either way, they’re on the right track, and I’m genuinely looking forward to what future certifications have in store. Keep it up!